Cloud adoption continues to accelerate across both public and private sectors, and cloud spending has now reached a scale where cost management is a strategic and board-level concern rather than a purely technical issue.
A Gartner study published in late 2024 projected that global public cloud end-user spending would reach approximately USD 723 billion in 2025, underpinned by sustained double-digit growth driven by digital transformation initiatives, large-scale data platforms and accelerating AI adoption.
As organisations enter 2026, cloud is no longer an experimental or discretionary technology choice. It is a core operational dependency underpinning digital services, analytics, AI delivery and mission-critical systems. As a result, cloud costs now represent a material and recurring component of IT, transformation and operational budgets.
At the same time, there is strong and consistent evidence that a significant proportion of cloud spend does not deliver corresponding business value. IDC estimates that 20-30% of all cloud spending is wasted, even in organisations with established cloud platforms and governance practices.
A 2024 cloud efficiency study referenced by Stacklet found that 78 percent of organisations estimate that between 21 and 50 percent of their annual cloud spend is wasted, with many losing more than USD 75,000 per month due to idle resources, inefficient architectures and weak controls.
In 2026, cloud cost optimisation is therefore no longer about reactive cost cutting or short-term savings. It is about financial sustainability, architectural resilience, responsible AI adoption and long-term operational maturity. Organisations that fail to embed cost optimisation into day-to-day cloud operations risk limiting innovation, constraining AI initiatives and eroding confidence at executive and assurance levels.
This guide sets out practical, execution-focused cloud cost optimisation strategies for 2026, combining industry research, FinOps best practice and real-world delivery experience across complex cloud estates.
A practical cloud cost optimisation roadmap for 2026
One of the most common reasons cloud cost optimisation initiatives fail is a lack of sequencing. Organisations often attempt to optimise everything at once, resulting in fragmented effort and limited impact. Successful programmes instead follow a phased approach aligned to FinOps maturity models and operational reality.
Phase 1: Visibility and accountability (weeks 0–4)
The objective of this phase is to understand where cloud spend occurs and who is responsible for it.
Key activities include:
- defining a consistent, mandatory tagging standard
- allocating cloud costs to services, teams and business units
- establishing baseline dashboards, budgets and alerts
Without this foundation, optimisation efforts lack focus and accountability.
Phase 2: Waste removal and early savings (months 1–3)
Once visibility exists, most organisations can realise rapid savings by addressing obvious inefficiencies.
Typical actions include:
- identifying idle, unused or oversized resources
- rightsizing the highest-cost services
- shutting down non-production environments outside working hours
This phase often delivers visible savings within weeks, helping to build organisational momentum.
Phase 3: Structural and architectural optimisation (months 3–9)
This phase addresses systemic inefficiencies that drive recurring cloud cost.
Key activities include:
- introducing auto-scaling and demand-based architectures
- applying savings plans and reserved capacity where usage is stable
- modernising legacy applications that were lifted and shifted without redesign
Phase 4: Prevention, governance and forecasting (ongoing)
Long-term value comes from preventing waste from re-emerging.
This requires:
- embedding a FinOps operating model
- automating cost guardrails and policy enforcement
- forecasting cloud spend based on business demand rather than historical usage
Why cloud cost optimisation matters in 2026
While cloud growth and waste provide the backdrop, several 2026-specific factors have increased the urgency of cost optimisation.
Cloud spend is now structurally embedded
With global cloud spending measured in hundreds of billions of dollars annually, cloud services now represent a permanent operating cost rather than a variable experiment. In 2026, optimisation must be treated as a continuous operational discipline, not a periodic financial exercise.
AI significantly increases cost pressure
AI and advanced analytics workloads are among the fastest-growing contributors to cloud spend. Model training, inference pipelines, vector databases and large-scale data storage require sustained compute, specialised GPUs and high-throughput data movement. Industry analysis reported by TechMonitor highlights AI adoption as a growing driver of cloud overspend when governance is weak
Visibility and governance remain inconsistent
FinOps Foundation surveys consistently show that more than 40 percent of organisations struggle to accurately attribute cloud spend, particularly across hybrid and multi-cloud estates. Without clear ownership, optimisation initiatives lose traction.
Public sector accountability continues to increase
UK government guidance on cloud usage emphasises transparency, value for money and responsible stewardship of public funds. In 2026, demonstrable control over cloud cost is essential for audit readiness, regulatory compliance and maintaining public trust.
Key cloud cost trends shaping 2026
Across analyst research, FinOps community insights and delivery experience, several structural trends are shaping cloud economics in 2026. These trends explain why cloud costs remain difficult to control, even as tooling, skills and platform maturity improve.
Despite years of investment in cloud platforms, cost visibility tools and FinOps capability, cloud waste remains consistently high. This is not primarily due to technical immaturity, but because cloud operating models still incentivise speed and autonomy over financial discipline. Teams are optimised to deliver features quickly, while the financial impact of architectural decisions often remains abstract or delayed.
In 2026, waste increasingly originates from design-time decisions, such as selecting always-on services for variable workloads, duplicating datasets for convenience, or over-allocating resources to avoid performance risk. This shifts optimisation from a purely operational activity to a design and governance challenge, where cost awareness must be embedded earlier in the delivery lifecycle.
AI and data platforms are redefining what “expensive” means in cloud
Historically, cloud cost growth was driven by general-purpose compute and storage. In 2026, the cost profile will be increasingly shaped by specialised, high-performance services. GPU-backed workloads, vector databases, real-time analytics engines and large-scale data pipelines now dominate spend growth, particularly in organisations scaling AI beyond experimentation.
This trend is significant because these workloads behave differently from traditional applications. They are data-intensive and highly sensitive to architectural choices, meaning small design inefficiencies can have disproportionate cost impact. As a result, organisations are finding that traditional optimisation levers are less effective unless they are complemented by AI-aware financial governance and forecasting models.
FinOps is shifting from insight to intervention
FinOps adoption has moved beyond dashboards and retrospective reporting. In 2026, leading organisations will be using FinOps as an active control mechanism, not just an analytical function. This includes embedding financial signals into delivery pipelines, using cost data to inform architectural trade-offs, and aligning spend decisions with business priorities in near real time.
This shift reflects a broader recognition that cost is a first-class operational metric, alongside reliability, security and performance. As FinOps matures, its value increasingly depends on organisational influence and integration, rather than tooling sophistication alone. The challenge for many organisations is no longer visibility but turning insight into enforceable decisions without slowing delivery.
Multi-cloud complexity is now an economic issue, not just a technical one
Multi-cloud strategies have become standard, driven by resilience, policy, supplier strategy and workload suitability. However, in 2026 the cost implications of multi-cloud are becoming more visible. Differences in pricing models, discount structures, data egress costs and managed services make consistent optimisation across providers difficult.
As a result, organisations are increasingly forced to balance strategic flexibility against economic efficiency. This has elevated the importance of cross-cloud financial normalisation, where spend is compared and governed at a service or capability level rather than by provider. Cost optimisation in multi-cloud environments is therefore becoming a portfolio management challenge, not just a technical exercise.
Public sector collaboration is moving from policy to practice
In the public sector, cloud cost management is evolving from guidance and principle-based frameworks into practical, shared implementation. Departments and agencies are increasingly collaborating on standards for cost transparency, FinOps maturity and data sharing, supported by central initiatives and communities of practice.
This trend reflects growing recognition that cloud cost challenges are systemic, not isolated. By sharing tooling patterns, metrics and governance approaches, public sector organisations aim to reduce duplication, improve comparability and strengthen assurance. In 2026, this collective approach is becoming a key enabler of sustainable cloud adoption, particularly as AI and data workloads expand across government.
These trends manifest in a set of recurring challenges that organisations encounter as cloud estates scale.
Common cloud cost optimisation challenges
Despite growing awareness of cloud economics and wider adoption of FinOps practices, many organisations continue to struggle with the same underlying cost challenges. In 2026, these issues persist not because of a lack of technology, but because cloud cost management is as much an organisational and operating-model problem as it is a technical one.
1. Poor visibility and inconsistent allocation
While most organisations collect cloud cost data, many still lack decision-grade visibility. Costs are often visible at an account or subscription level, but not consistently attributed to business services, products or outcomes. This creates a disconnect between cloud consumption and business value.
In practice, visibility breaks down when tagging standards are inconsistently applied, ownership is unclear, or cost data is interpreted differently by engineering, finance and product teams. In 2026, this challenge is compounded by the rise of shared platforms, managed services and AI pipelines, where multiple teams consume the same underlying resources. Without a common allocation model, cloud spend becomes difficult to explain, challenge or forecast, even when dashboards and detailed receipts exist.
The result is a familiar pattern: cost reports are produced, but they do not meaningfully influence decisions.
2. Idle and over-provisioned resources
Idle and over-provisioned resources remain one of the most visible sources of cloud waste, yet they continue to accumulate in mature environments. This is partly because cloud platforms make it easy to provision capacity quickly, but place relatively little friction on leaving it running indefinitely.
In many organisations, responsibility for decommissioning resources is ambiguous. Development and test environments are created for short-term needs but persist long after projects move on. Capacity is deliberately oversized to reduce perceived performance risk, particularly for customer-facing or data-intensive workloads. Container platforms add another layer of abstraction, where unused capacity is less obvious than in traditional virtual machine estates.
By 2026, the challenge is less about identifying individual idle resources and more about preventing sprawl from becoming the default state of cloud environments.
3. Lift-and-shift migrations
Many organisations still operate a significant proportion of workloads that were migrated to the cloud using lift-and-shift approaches. While this accelerates migration timelines, it often locks in cost inefficiencies that persist for years.
Applications designed for on-premise infrastructure typically assume static capacity, peak sizing and tightly coupled components. When moved unchanged to the cloud, these assumptions translate into always-on resources, limited elasticity and higher baseline costs. Over time, teams compensate by over-provisioning to maintain stability, rather than addressing architectural limitations.
In 2026, the challenge is that these workloads often underpin critical services. Their cost impact is well understood, but the perceived risk and effort of refactoring mean optimisation is repeatedly deferred, even as they consume a disproportionate share of cloud budgets.
4. Limited governance and automation
Cloud environments scale faster than traditional governance models. Where policies, approvals and controls rely on manual processes, they quickly become bottlenecks and are either bypassed or ignored.
In many organisations, governance is still applied after resources are provisioned, rather than embedded into how platforms are built and used. This leads to inconsistent enforcement of standards, reactive clean-up exercises and reliance on individual diligence rather than systemic control.
By 2026, the absence of automation will become a cost challenge. Without automated guardrails, organisations struggle to maintain consistent financial control as teams, workloads and environments grow. The result is a cycle of periodic optimisation efforts that temporarily reduce spend, only for inefficiencies to re-emerge.
5. AI and data gravity
AI and data-driven workloads introduce a distinct set of cost challenges that differ from traditional application hosting. These workloads are inherently data-intensive, often requiring large datasets to be moved, duplicated or processed repeatedly across environments.
As models evolve and pipelines become more complex, storage volumes grow, GPU utilisation increases and data transfer costs become more material. Data gravity exacerbates this effect, making it difficult to relocate workloads without incurring additional cost or performance penalties. In many cases, teams optimise for experimentation speed rather than cost efficiency, particularly in early AI adoption phases.
In 2026, organisations are finding that AI cost challenges are not caused by individual services, but by end-to-end pipeline design, where small inefficiencies compound across storage, compute and data movement over time.
Why these challenges persist
Taken together, these challenges highlight a common theme: cloud cost optimisation fails when it is treated as a periodic clean-up activity rather than a core operating discipline. Without clear ownership, aligned incentives and embedded governance, inefficiencies naturally re-emerge as cloud estates and AI workloads continue to scale.
Cloud cost optimisation strategies and best practices for 2026
1. Improve tagging, allocation and cost visibility
What to do
Building on the visibility foundation outlined earlier, define a mandatory tagging standard covering application, owner, environment, cost centre, data classification and compliance context.
How to implement
- enforce tagging using cloud-native policy tools
- validate tags in CI/CD pipelines
- auto-remediate missing metadata
What good looks like
- over 90 percent of cloud spend accurately tagged
- monthly showback or chargeback reporting
- clear ownership of top cost drivers
Organisations often establish this capability as part of a broader cloud landing zone or cloud engineering programme.
2. Adopt continuous rightsizing
Rightsizing should be an ongoing operational activity rather than an annual review.
Effective approaches include:
- monthly utilisation reviews
- thresholds such as CPU below 30 percent or memory below 40 percent for sustained periods
- removal of unused snapshots and volumes
This approach consistently delivers savings without service degradation.
3. Use auto-scaling and demand-based architectures
Auto-scaling ensures capacity aligns with actual demand.
Best practice includes:
- horizontal scaling for stateless services
- defined minimum and maximum capacity limits
- regular load testing
- automatic shutdown of non-production environments outside business hours
These patterns are commonly implemented during platform migration and modernisation initiatives.
4. Optimise storage and data lifecycle management
Storage costs grow rapidly, particularly for analytics and AI.
Effective strategies include:
- tiering infrequently accessed data
- enforcing retention and lifecycle rules
- archiving logs
- reducing unnecessary cross-region transfers
These controls are often embedded within data platform and analytics architectures.
5. Align purchasing models with workload patterns
Savings plans and reserved capacity can reduce long-running workload costs by 30–70 percent when applied correctly.
Best practice includes:
- committing only once usage patterns stabilise
- targeting utilisation above 70 percent
- reviewing commitments quarterly
6. Build a mature FinOps operating model
A mature FinOps model includes:
- a central FinOps capability
- real-time dashboards
- shared accountability across engineering, finance and product teams
- monthly governance reviews
- demand-based forecasting
Many organisations formalise this capability as a dedicated FinOps and cost optimisation function.
7. Modernise applications to remove architectural waste
Modernisation often delivers greater long-term savings than pricing optimisation alone.
Cloud-native patterns such as containers, serverless and managed services reduce reliance on persistent infrastructure and scale automatically with demand.
8. Optimise AI and advanced analytics workloads
AI workloads require dedicated optimisation strategies.
Effective techniques include:
- using lower-cost GPU types for development and testing
- separating training and inference environments
- tracking cost per inference and cost per model version
- pruning unused models and datasets
- monitoring vector database growth carefully
9. Automate cost guardrails
Automation prevents waste before it accumulates.
Examples include:
- enforcing tagging automatically
- shutting down idle environments
- blocking unapproved high-cost services
- detecting anomalous spend
- automatically cleaning up unused resources
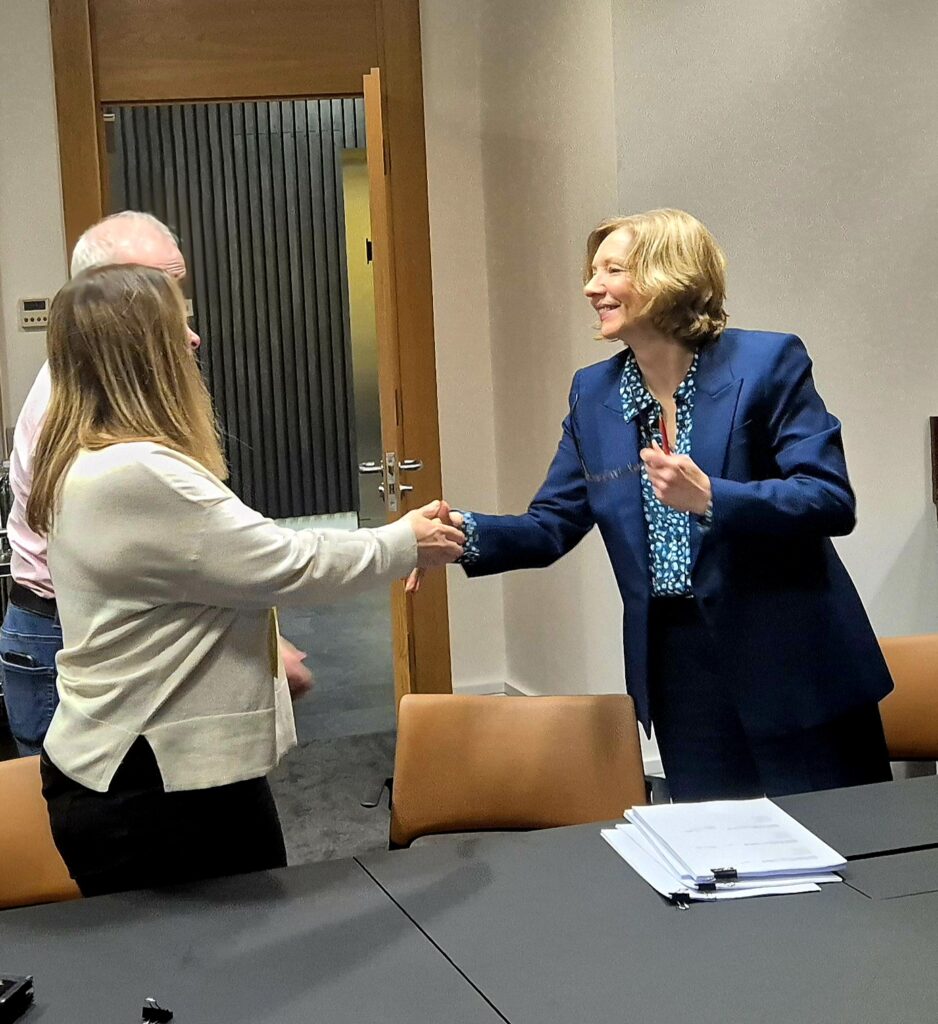
Cloud cost optimisation with CACI
In 2026, cloud cost optimisation is about predictability, resilience and sustainable innovation, not reactive cost cutting. CACI supports organisations across the full optimisation lifecycle, from rapid waste reduction to long-term architectural transformation and FinOps maturity.
If your organisation cannot clearly explain who owns cloud spend, why costs fluctuate month-to-month, or how AI growth will be funded sustainably, optimisation opportunities already exist. CACI helps organisations move from reactive cost control to value-driven cloud economics that support growth, innovation and public accountability.
FAQs around cloud cost optimisation strategies
What does a cloud cost optimisation strategy include in 2026?
A cloud cost optimisation strategy in 2026 includes cost visibility, architectural efficiency, governance and forecasting, enabling organisations to control spend while scaling cloud and AI workloads. It focuses on embedding cost awareness into design, delivery and operational decision-making rather than reactive clean-up.
How is cloud cost optimisation different from FinOps?
Cloud cost optimisation focuses on reducing waste and improving efficiency, while FinOps is the operating model that makes those improvements sustainable. FinOps aligns engineering, finance and product teams around shared accountability, governance and forecasting.
When should organisations start optimising cloud costs?
Organisations should start optimising cloud costs as soon as cloud usage begins, not after spend becomes excessive. Early optimisation prevents inefficient patterns becoming embedded and reduces long-term cost growth.
How much can organisations save with cloud cost optimisation?
Most organisations can reduce cloud spend by 20 to 40 percent through effective cost optimisation, depending on estate maturity and governance. Savings are highest where idle resources, over-provisioning and legacy workloads are common.
Why do cloud costs keep increasing even after optimisation?
Cloud costs continue to increase when optimisation focuses on one-off savings rather than ongoing governance and demand-based control. New services, data pipelines and AI workloads often grow faster than financial controls evolve.
How do AI workloads affect cloud cost optimisation?
AI workloads increase cloud costs because they rely on high-performance compute, large datasets and repeated processing, which scale non-linearly. This requires AI-specific cost governance and forecasting to remain sustainable.
Is cloud cost optimisation harder in multi-cloud environments?
Cloud cost optimisation is harder in multi-cloud environments because pricing models, discounts and data transfer costs vary across providers. Organisations increasingly manage costs at a service or portfolio level rather than optimising each cloud independently.
Who should own cloud cost optimisation?
Cloud cost optimisation should be a shared responsibility across engineering, finance and product teams, coordinated by a central FinOps or governance function. This ensures cost decisions align with technical and business priorities.
How often should cloud cost optimisation be reviewed?
Cloud cost optimisation should be reviewed continuously using real-time monitoring, with formal governance reviews conducted monthly. This combination enables early detection of anomalies while supporting strategic oversight.