Networking is continuing to show remarkable advances, marked by emerging technologies such as AI and network-specific LLMs, with changing business demands that are paving the way for a more secure and connected future.
Businesses and industries that recognise the power of adopting these evolving networking technologies and best practices in improving their performance will set themselves up for unparalleled future growth, solution scalability and competitiveness. Those that don’t are increasingly getting left behind.
So, what are the main networking trends that we have seen in 2025?
Advanced 5G
Unlike its 4G and 3G predecessors, the availability of industrialised, private 5G offerings – acting as a more-capable, longer-reaching alternative to wi-fi in specific building scenarios – is leading to the global 5G services market is set to reach an annual growth rate of 59.4% by 2030. 2025 has been particularly pivotal for 5G, with the introduction of 5.5G (also known as 5G Advanced) bringing increased speeds and functionalities set to be deployed in some of the world’s leading markets this year.
Network services have had to make way for the increased bandwidth and low latency that has come from the rollout of 5G, ensuring a smooth and responsive user experience and the ability to connect even more devices within a small area without compromising on performance. These capabilities have augmented the likes of IoT devices and virtual reality (VR) applications, which require speedy transfer and real-time communication. We expect trends such as VR and augmented reality (AR) – such as the Apple Visio Pro – to accelerate the dependence on not only bandwidth (speed) in networking, but also in latency (lag); the latter of which has often been neglected by many enterprise networking technologies.
Edge computing migration
Despite its industry presence for years now, edge computing has been gaining prominence in 2025 as a means to support organisations with processing their data closer to the sources of data or users—at the edge of the network. What’s old is in many ways new again, with the content delivery network (CDN) coming back to the fore as a primary on-ramp into public cloud and other aggregated network ecosystems and walled gardens. Both edge and CDN minimise latency and enhance real-time processing capabilities that are not possible purely via the public cloud. By processing data at the edge of the network, the strain on network bandwidth is also alleviated.
Edge computing will continue influencing network architecture design and redefining the parameters of data processing with the development of smart cities, IoT and AI-powered applications that rely on data processing, with businesses strongly encouraged to migrate workloads to edge computing. The aforementioned 5.5G (5G Advanced) rollout this year directly embeds data centres into telecom networks, reducing latency and enhancing compliance in doing so.
Multi-cloud networking and environments
As of 2025, single-cloud networking has become much less common for enterprises, with multi-cloud networking (MCN) and environments at the forefront. Compared to the singular platform and vendor approach, multi-cloud networking and environments consist of many tools and solutions that enable networking and connectivity across cloud environments. They mitigate the limitations that come with using traditional network architecture by allowing for seamless integration across multiple cloud environments.
The key challenge we see in our customer base with multi-cloud networking is the sheer amount of complexity and same-but-different solutions within constructs such as cloud networking, underlay networking and overlay networking. Many customers will have multi-cloud through necessity rather than strategy – for instance, using Microsoft Cloud for Office365 collaboration, alongside AWS for developer-led public cloud and likely a smattering of other PaaS and SaaS cloud offerings. We’re increasingly seeing the rise of cloud exchange gateways as an alternative to Internet exchange (IX), bringing the same complexity of IX management – such as peering management, route policy and the like – down from the ISP domain and into the enterprise domain.
By 2031, the global market size of multi-cloud networking is projected to reach $19.9 billion USD (£15.7 billion) and grow at a rate of 23.3%. Businesses that embrace multi-cloud networking and environments will find themselves connecting and managing workloads across diverse cloud environments and establishing a secure, high-performance network that will carry out operations as efficiently as possible, steadily flow data between clouds to reduce data silos, optimise data transmission speeds for faster response times and improve customer experiences by evolving along with users.
AI networking & AIOps
Of all the trends unfolding in the networking space this year, AI is proving to be a substantial one. Networking solutions have become increasingly reliant upon artificial intelligence (AI) for optimisation, maintenance and analytical purposes. AI networking has also bolstered capabilities within industries like network services to develop robust and efficient networks that will continue to support operations.
Trends such as network observability and network telemetry mean the amount of logging, traces and metrics required to be analysed is becoming untenable for any one human. AIOps is becoming a necessity to augment overworked and often under-tooled network operations staff in delivering, maintaining and optimising increasingly agile, complex and demanding enterprise networks. Into 2025, it helps operations staff prevent faults and detect anomalies or unusual movement, adjust capacity in line with demand and monitor configuration against regulatory standards.
By continuously influencing how networking infrastructure is built and integrating into network automation tools to enhance decision-making and analyses, AI is proving to be a game-changer when it comes to networking. We’re finding several amazing use cases where the use of an AI tool, such as GPT, enables us to grok an API with a contextually-specific use case, or quickly glean through pages of troubleshooting documentation to find the exact nuance of bug, CVE or PSIRT we’re in the midst of fixing or coding.
To learn more about the impact of AI on networking through 2025, take a look at our blog on the top network automation trends.
Intent-based networking (IBN)
Intent-based networking (IBN) has been a groundbreaking networking advancement thanks to its ability to use automation and artificial intelligence (AI) to simplify network management. This technology has rapidly grown in popularity for networking-oriented businesses, as it allows administrators to define a network’s intent and automatically translate and implement these intentions across the wider network infrastructure to optimise its performance, security and scalability.
IBN eliminates the need for manual configuration—often a requirement of traditional networks– through its automated processing that is based on real-time analytics, ultimately improving efficiency while decreasing the margin of error and revolutionising the ways in which businesses can streamline their network management.
While still not mature, the concepts of IBN are finding their way into mainstream NMS, OSS – and increasingly even ITSM products, and matching the “as a service” patterns application development teams are used to from the public cloud world.
How CACI can support your networking journey
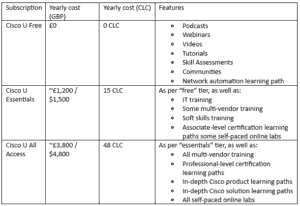
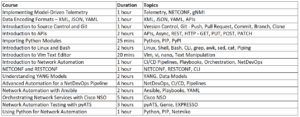
At CACI, our trained cohort of network automation engineers, network reliability engineers (NREs) and consultants are well versed in a plethora of IT, networking and cloud technologies, ready and willing to share their industry knowledge to benefit your unique networking requirements.
We act as a trusted advisor to help your organisation drive better experiences by enabling more effective use of technology and business processes. Our in-house experts have architected, designed, built and automated some of the UK’s largest enterprise networks and data centres. From NSoT through CI/CD, version control, observability, operational state verification, network programming and orchestration, our expert consulting engineers have architected, designed, built and automated some of the UK’s largest enterprise, service provider and data centre networks, with our deep heritage in network engineering spanning over 20 years.
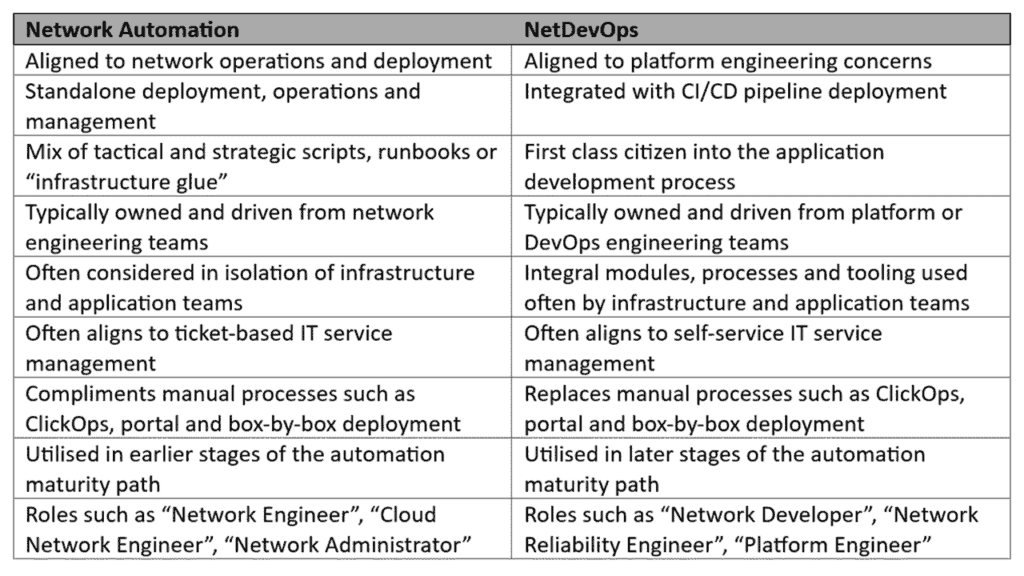
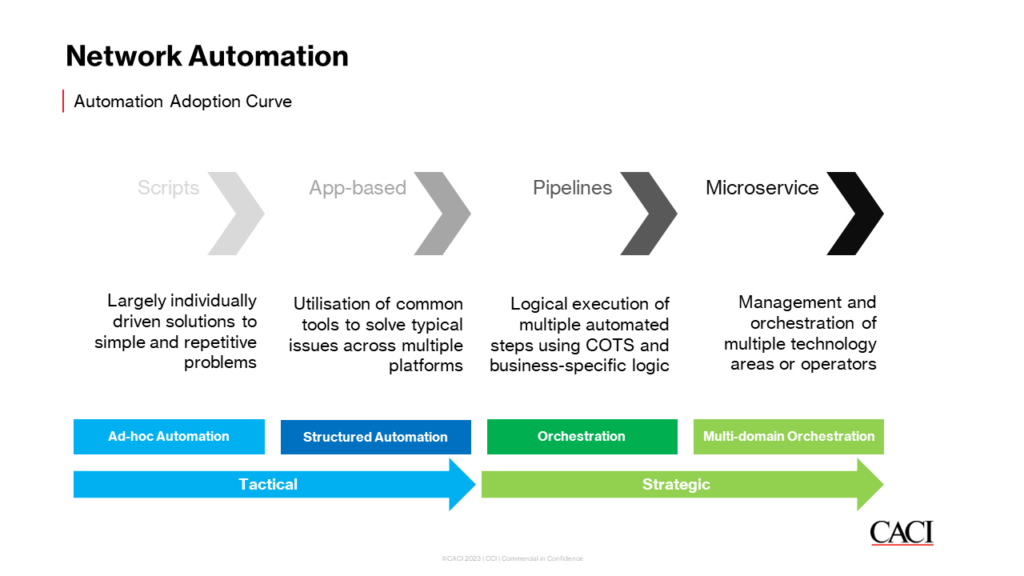
Take a look at Network Automation and NetDevOps at CACI to learn more about some of the technologies, frameworks, protocols and capabilities we have, from YAML, YANG, Python, Go, Terraform, IaC, API, REST, Batfish, Git, NetBox and beyond.
Find out more about enhancing your networking journey by getting in touch with us today.